Server Management
5/8/2026
Critical cPanel & WHM Vulnerability CVE-2026-41940 – Immediate Security Update Required
A critical authentication bypass vulnerability affecting cPanel & WHM has been actively exploited in the wild. Learn how to secure your server, apply emergency updates, rotate SSH keys, and detect possible compromise indicators.
Critical cPanel & WHM Security Vulnerability (CVE-2026-41940) – Immediate Action Required
Millions of Servers Potentially at Risk
A critical security vulnerability identified as CVE-2026-41940 has recently affected cPanel & WHM servers worldwide. The vulnerability carries a CVSS score of 9.8, making it one of the most severe cPanel security incidents in recent years.
Security researchers and hosting providers have confirmed that the vulnerability has already been actively exploited in the wild before the official public disclosure.
Administrators using cPanel & WHM are strongly advised to update their servers immediately.
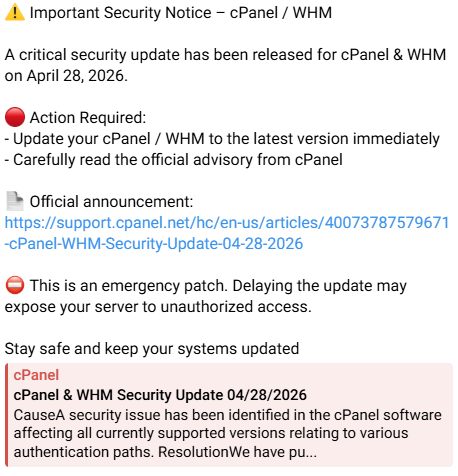
Official cPanel Security Advisory
cPanel officially released an emergency security advisory and patched versions on April 28, 2026.
Official advisory:
The vulnerability impacts:
- cPanel
- WHM (Web Host Manager)
- DNSOnly
- WP Squared (WP2)
What is CVE-2026-41940?
CVE-2026-41940 is a critical authentication bypass vulnerability affecting cPanel & WHM.
The vulnerability allows unauthenticated remote attackers to bypass authentication and potentially gain administrative access to the server without valid credentials.
Researchers identified that the issue originates from improper session handling and insufficient sanitization during authentication processing.
If successfully exploited, attackers may:
- Gain unauthorized WHM access
- Execute malicious commands
- Access hosted websites and databases
- Install malware or botnets
- Steal credentials and SSH keys
- Deploy ransomware
- Delete or manipulate server data
- Use the server for spam or attacks
According to multiple security reports, exploitation activity had already started weeks before the public disclosure.
Patched cPanel Versions
cPanel has released patched versions for all supported branches.
Fixed Versions
- 11.110.0.97
- 11.118.0.63
- 11.126.0.54
- 11.130.0.18
- 11.132.0.29
- 11.134.0.20
- 11.136.0.5
Any server running versions older than the patched releases should be considered vulnerable.
Signs of Active Exploitation
Several hosting providers and cybersecurity researchers observed active exploitation attempts targeting unpatched servers.
Some attacks reportedly involved:
- Downloading malicious binaries
- Installing botnets
- Reading sensitive server files
- Accessing SSH keys
- Modifying permissions
- Re-downloading malware after deletion
- Performing reconnaissance on hosting accounts
Important Immediate Actions
1. Update cPanel Immediately
This is the highest priority action.
Do not delay updates.
2. Rotate All Passwords
If the server was exposed:
- Change WHM root password
- Reset all reseller passwords
- Reset cPanel account passwords
- Rotate database passwords
- Update API tokens
- Reset FTP credentials
3. Replace SSH Keys
Attackers may have accessed:
/root/.ssh/id_rsa/root/.ssh/authorized_keys
Generate new SSH keys and revoke old ones immediately.

 INR
INR
 USD
USD
 MYR
MYR

